So I ran into an interesting situation when we started deploying Windows 7 out via OSD to Windows XP boxes recently. There were some PCs that would take FOREVER to download the image, which would actually end up failing the task sequence. What I ended up finding out was that these computers (Dell Optiplex 960’s) were set to use IDE in the BIOS, which set me out on the task of finding the fastest way to add a step to my task sequence to modify the BIOS during an OSD pushed OS upgrade. I looked into modifying the PE so that the change could be done from the BIOS, but in the time constraint I was working under I ended up simply installing the Dell Open Manage Client Instrumentation 8 (available here) on the Windows XP workstation and changing it before it was shut down as a part of the task sequence.
First, I created a task folder that checked if it was a 960 using a WMI model query:
Select * From Win32_ComputerSystem WHERE Model LIKE “%optiplex 960%”

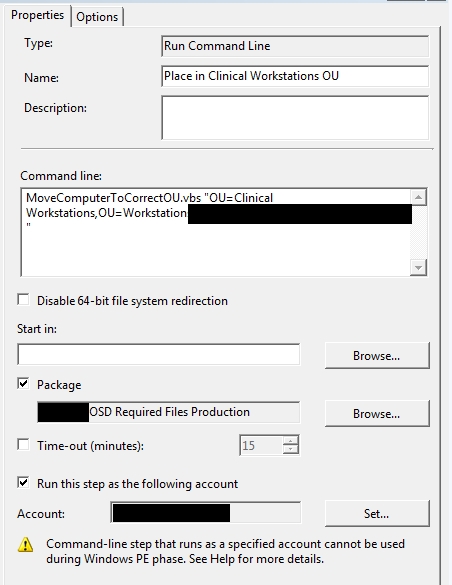
Then I installed the open manage client, then set the bios. My command lines for my 2 tasks were:
OM_APP_WIN_R300391.EXE /s
And
cscript.exe OMCI_SATA_Operation.vbs 4
The referenced OMCI_SATA_Operation.vbs script is actually a modified script file (Original name is OMCI_BIOS_ACHI.vbs) available in the package files of the open manage client. When running this script, the option 4 was used to set it to AHCI.
And presto! Since I had to gather information from the OS that was about to be reimaged anyway, this was an option for me. However, for other options like USB deployment and situations where the pre-existing OS might not be available, this will not be the best option. This was a quick and dirty method, but worked during the rollout.
Here is the modified script text:
‘**********************************************************************
‘*** Name: OMCI_BIOS_AHCI.vbs
‘*** Purpose: To clear the chassis intrusion status on a Dell OMCI client.
‘*** Usage: cscript.exe //nologo OMCI_BIOS_AHCI.vbs <systemname>
‘***
‘*** This sample script is provided as an example only, and has not been
‘*** tested, nor is warranted in any way by Dell; Dell disclaims any
‘*** liability in connection therewith. Dell provides no technical
‘*** support with regard to such scripting. For more information on WMI
‘*** scripting, refer to applicable Microsoft documentation.
‘*** NOTE: Replace <Password> in line 57 (inside the quotes)
‘*** with the desired values if there is any password set in the system.
‘*** If both passwords(Admin and Boot) are set please replace it with Admin Password.
‘*** If there is no password set in the system please leave it as empty.
‘**********************************************************************
Option Explicit
‘*** Declare variables
Dim strNameSpace
Dim strComputerName
Dim strClassName
Dim strKeyValue
Dim objInstance
Dim strPropName
Dim strPropValue
Dim oInParams
Dim objWMIService
Dim returnValue
Dim ColSystem
Dim strAttributeName(2)
Dim strAttributeValue(2)
‘*** Check that the right executable was used to run the script
‘*** and that all parameters were passed
If (LCase(Right(WScript.FullName, 11)) = “wscript.exe” ) Or _
(Wscript.Arguments.Count < 1) Then
Call Usage()
WScript.Quit
End If
‘*** Initialize variables
strNameSpace = “root/dcim/sysman”
strComputerName = “.”
strClassName = “DCIM_BIOSService”
strAttributeName(0) = “Embedded SATA Controller”
strAttributeValue(0) = WScript.Arguments(0)
‘*** All possible values for Embedded SATA Controller are as follows:
‘*** Possible values are:
‘*** 1 – Off
‘*** 3 – ATA
‘*** 4 – AHCI
‘*** 5 – RAID
returnValue = 0
‘*** Retrieve the instance of DCIM_BIOSService class
Set objWMIService = GetObject(“winmgmts:{impersonationLevel=impersonate,” &_
“AuthenticationLevel=pktprivacy}\\” & strComputerName & “\” &_
strNameSpace)
Set ColSystem=objWMIService.execquery (“Select * from ” & strClassName)
For each objInstance in ColSystem
Set oInParams= objInstance.Methods_(“SetBIOSAttributes”).InParameters.SpawnInstance_
oInParams.AttributeName = strAttributeName
oInParams.AttributeValue = strAttributeValue
Set returnValue = objInstance.ExecMethod_(“SetBIOSAttributes”, oInParams)
Next
‘*** If any errors occurred, let the user know
If Err.Number <> 0 Then
WScript.Echo “Changing BIOS SATA operation failed.”
End If
‘*** Sub used to display the correct usage of the script
Sub Usage()
Dim strMessage
strMessage = “incorrect syntax. You should run: ” & vbCRLF & _
“cscript.exe /nologo OMCI_SATA_Operation.vbs <Possible Sata Value>. All possible values for Embedded SATA Controller in OMCI 8 are as follows: 1 – Off,3 – ATA, 4 – AHCI, 5 – RAID”
WScript.Echo strMessage
End Sub